How to Set Up Automated Incident Escalation Workflows in 2026
Learn to build bulletproof escalation workflows that automatically route critical incidents to the right teams. Master timing, triggers, and communication flows.
TL;DR: Automated incident escalation workflows ensure critical issues reach the right people at the right time. This guide covers trigger setup, escalation chains, timing intervals, communication channels, and testing procedures to minimize downtime and improve response times.
Why Automated Escalation Matters More Than Ever
In 2026, downtime costs businesses an average of $9,000 per minute. Manual escalation processes simply can't keep pace with the speed modern systems require.
Automated escalation workflows act as your digital safety net. When a critical incident occurs at 3 AM, your workflow immediately notifies the on-call engineer, escalates to management if unacknowledged, and keeps stakeholders informed — all without human intervention.
The difference between a 5-minute outage and a 2-hour disaster often comes down to how quickly incidents reach the right people.
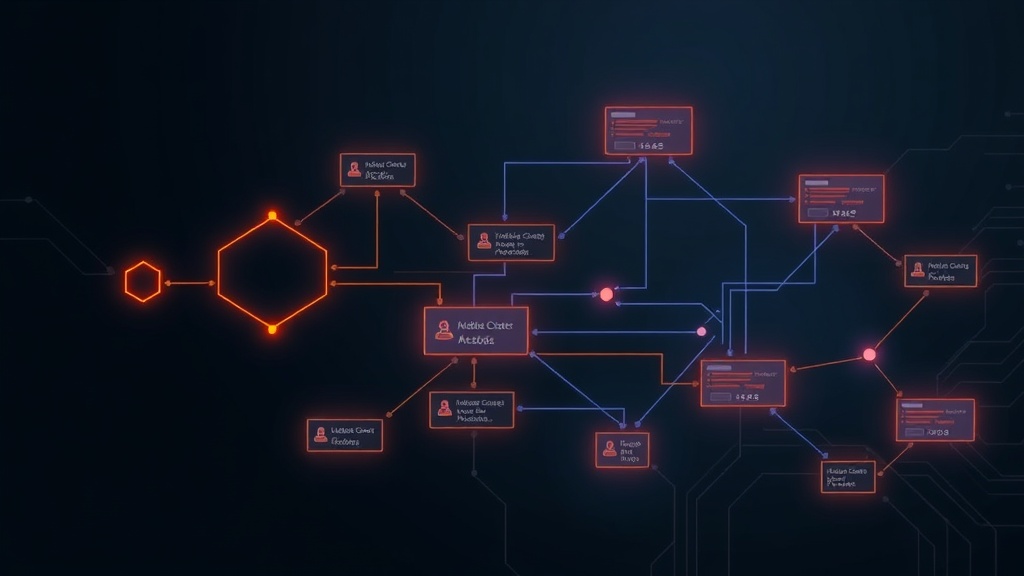
Understanding Escalation Workflow Components
Trigger Conditions
Your escalation workflow needs clear trigger conditions that define when to activate. Set these based on:
- Severity levels: Critical, high, medium, low incidents
- Service impact: Customer-facing vs internal systems
- Duration thresholds: Incidents lasting longer than X minutes
- Business hours: Different rules for peak vs off-peak times
For example, trigger immediate escalation for any customer-facing service showing 50%+ error rates, but use longer delays for internal development tools.
Escalation Chains
Design your escalation chain with multiple tiers:
- Primary responder: On-call engineer or specific team member
- Secondary responder: Team lead or backup engineer
- Management tier: Engineering manager or department head
- Executive tier: CTO or VP of Engineering (for major incidents only)
Keep each tier focused. Too many people in early stages creates noise and confusion.
Timing Intervals
Set realistic acknowledgment timeframes for each tier:
- Tier 1: 5-10 minutes during business hours, 15 minutes after hours
- Tier 2: 10-15 minutes during business hours, 20 minutes after hours
- Tier 3: 20-30 minutes regardless of time
- Tier 4: 30-45 minutes for executive involvement
Adjust these based on your team's response patterns and SLA requirements.
Setting Up Your Workflow Architecture
Choose Your Escalation Platform
Most modern incident management platforms offer built-in escalation features. Popular options include:
- PagerDuty: Comprehensive escalation policies with complex routing
- Opsgenie: Flexible scheduling with advanced notification rules
- VictorOps/Splunk: Integration-heavy approach for existing Splunk users
- Built-in monitoring tools: Many status page solutions like Livstat include escalation workflows alongside monitoring
Configure Notification Channels
Diversify your notification methods to ensure messages get through:
- SMS: High-priority alerts that bypass do-not-disturb settings
- Phone calls: For critical incidents requiring immediate attention
- Email: Detailed incident information and documentation
- Slack/Teams: Real-time collaboration and status updates
- Push notifications: Mobile app alerts for on-the-go responders
Never rely on a single channel. Network issues, dead batteries, or simple human error can block any individual method.
Define Escalation Rules
Create specific rules for different scenarios:
Rule Example 1: Customer-Facing API Down
- Trigger: API response time > 10 seconds OR error rate > 25%
- Tier 1: API team on-call (immediate)
- Tier 2: Backend team lead (5 minutes if unacknowledged)
- Tier 3: Engineering manager (15 minutes)
- Tier 4: CTO (30 minutes)
Rule Example 2: Database Performance Degradation
- Trigger: Query response time > 2 seconds for 5+ minutes
- Tier 1: Database administrator (10 minutes)
- Tier 2: Infrastructure team (20 minutes)
- Tier 3: Senior DBA (35 minutes)
Implementation Best Practices
Start Simple, Then Iterate
Begin with basic escalation chains and refine based on real incidents. Complex workflows often fail because they're over-engineered from day one.
Your first workflow might be:
- Alert primary on-call
- Escalate to manager after 15 minutes
- Include executive team after 45 minutes
Add complexity only after testing this foundation thoroughly.
Account for Human Factors
People aren't robots. Build flexibility into your workflows:
- Vacation coverage: Automatic failover when primary responders are out
- Timezone considerations: Different escalation paths for global teams
- Skill-based routing: Route database issues to DBAs, not frontend developers
- Fatigue management: Rotate on-call duties to prevent burnout
Test Your Workflows Regularly
Schedule monthly escalation drills using synthetic incidents. Test:
- End-to-end notification delivery: Do messages reach everyone?
- Response time accuracy: Are people responding within expected timeframes?
- Communication clarity: Do responders understand the incident severity?
- Resolution tracking: Are incidents properly closed and documented?
Document what works and what doesn't. Failed drills provide valuable learning opportunities.
Advanced Workflow Features
Conditional Escalation
Set up smart escalation based on multiple conditions:
- Time-based: Different rules for weekends vs weekdays
- Incident type: Security incidents follow different paths than performance issues
- Service dependencies: Escalate faster for services with downstream impacts
- Customer impact: VIP customers trigger immediate executive notification
Auto-Resolution Integration
Connect your escalation workflow to automated remediation:
- Self-healing systems: Stop escalation if automated fixes resolve the issue
- Capacity scaling: Pause escalation during auto-scaling events
- Maintenance windows: Suppress non-critical escalations during planned maintenance
Cross-Team Coordination
Design workflows that span organizational boundaries:
- Customer support integration: Automatically notify support teams of customer-facing issues
- Marketing coordination: Include communications team for major outages
- Legal involvement: Escalate security incidents to legal and compliance teams
Measuring Escalation Effectiveness
Track key metrics to optimize your workflows:
Response Time Metrics
- Mean Time to Acknowledgment (MTTA): How quickly incidents get initial response
- Mean Time to Resolution (MTTR): Total time from incident to resolution
- Escalation frequency: Percentage of incidents requiring tier 2+ involvement
Quality Metrics
- False positive rate: Incidents that escalated unnecessarily
- Missed escalations: Critical incidents that should have escalated but didn't
- Communication effectiveness: Stakeholder satisfaction with incident updates
Operational Metrics
- On-call burden: Hours spent responding to incidents per team member
- After-hours escalations: Incidents requiring off-hours response
- Resolution accuracy: Percentage of incidents resolved by the correct team
Common Pitfalls and Solutions
Over-Escalation
Problem: Every minor issue reaches executives, creating alert fatigue.
Solution: Implement severity-based escalation with clear criteria. Reserve executive notifications for truly business-critical incidents.
Under-Escalation
Problem: Critical incidents sit unacknowledged because escalation rules are too lenient.
Solution: Shorten acknowledgment windows for high-severity incidents. Better to over-notify than miss a critical issue.
Communication Gaps
Problem: Escalation happens but context gets lost between tiers.
Solution: Standardize incident summaries and ensure each escalation includes full context, not just the alert.
Conclusion
Automated incident escalation workflows transform your incident response from reactive firefighting to proactive crisis management. Start with simple escalation chains, test thoroughly, and iterate based on real-world performance.
Remember: the best escalation workflow is one your team actually uses and trusts. Focus on reliability over complexity, and always prioritize getting the right information to the right people at the right time.
Your future self — and your customers — will thank you when that 3 AM critical incident gets resolved in minutes instead of hours.


